“A FREE IT ASSESSMENT FOR PHILADELPHIA OR PITTSBURGH!”
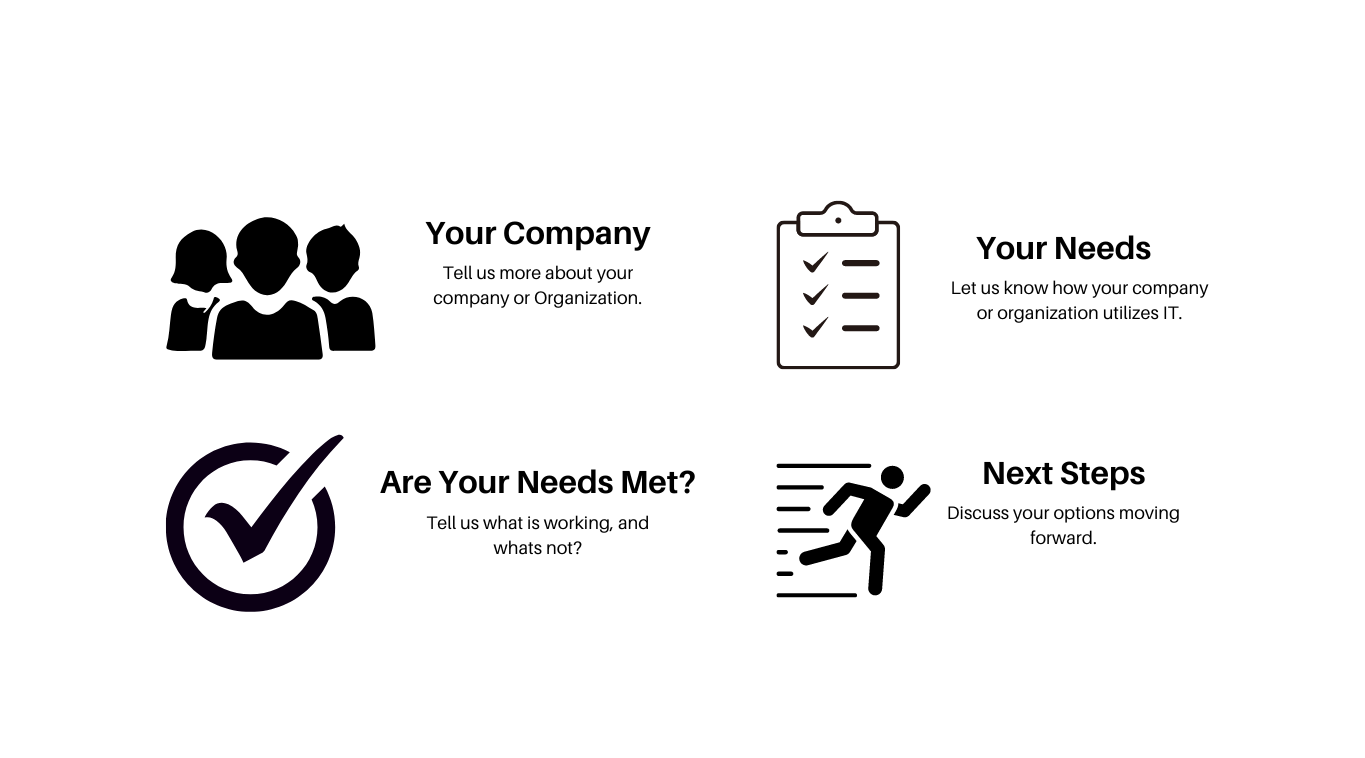
What You Can Expect?
This discovery call is the first step in your journey toward optimizing your current IT approach.
What Do I Get for Filling Out The Form?
- Free Network Evaluation: By completing the contact form, you unlock the opportunity to receive a complimentary network evaluation. Our team of experienced professionals will analyze your existing network architecture, identify potential vulnerabilities, and provide you with a comprehensive report. This evaluation will help you understand your current security posture and take proactive steps to enhance it.
- Customized Vulnerability Report: We believe in personalized solutions, and upon filling out the contact form, you will receive a customized report highlighting the specific vulnerabilities present within your infrastructure. This report will outline potential risks and provide actionable recommendations to mitigate them effectively. It will serve as a roadmap towards strengthening your organization’s security and data protection measures.
- Consultation to Address Your IT Needs: Our dedicated team will promptly reach out to you after receiving your contact form submission. We will schedule a call to discuss your unique IT requirements, challenges, and objectives. By understanding your organization’s goals, we can tailor our solutions to align perfectly with your business needs. This consultation ensures that we provide you with the most relevant and effective cybersecurity and IT services.
- Data Safety Assurance: Data breaches and cyber threats pose significant risks to businesses of all sizes. By reaching out to us through the contact form, you are taking a proactive step towards ensuring the safety and integrity of your valuable data. Our team will discuss data protection strategies, best practices, and industry-leading security measures to safeguard your sensitive information from unauthorized access, leaks, and breaches.
- Roadmap to a Safe and Secure Infrastructure: We understand that achieving a safe and secure IT infrastructure requires a well-defined plan. By filling out the contact form, you initiate the process of creating a roadmap that outlines the necessary steps to fortify your organization’s digital environment. We will work closely with you to develop a comprehensive plan that addresses your specific security needs, implements the latest technologies, and establishes protocols to maintain a resilient infrastructure.
Don’t delay in taking action to protect your organization’s digital assets.
Fill out our contact form today, and let Slick Cyber Systems be your trusted partner in strengthening your cybersecurity defenses, enhancing your information technology capabilities, and ensuring a safe and secure future for your business.
